How To Securely Connect Remote IoT Devices Using P2P SSH On Raspberry Pi
Imagine this: You're building an IoT project, but you're stuck trying to connect your Raspberry Pi to remote devices securely. Sound familiar? Well, buckle up because we're diving deep into the world of secure connections, peer-to-peer SSH, and making your IoT setup rock-solid. Whether you're a hobbyist or a pro, this guide will give you the tools to connect your Raspberry Pi remotely without compromising security.
Let's face it, in today's hyper-connected world, securing your IoT devices is not just a good idea—it's a necessity. From smart home gadgets to industrial sensors, every device needs to be locked down tight. That's where SSH comes in. But how do you make it work seamlessly across networks? We'll show you how to securely connect remote IoT devices using P2P SSH on Raspberry Pi, step by step.
This isn't just another tech tutorial. We'll cover everything from the basics of SSH and P2P networking to advanced configurations that'll make your setup bulletproof. So grab your Raspberry Pi, pour yourself a cup of coffee, and let's get started!
- Sundra Blustleaks The Untold Story Behind The Viral Sensation
- Avery Leigh Nude A Comprehensive Look Beyond The Clickbait
Why Secure Connections Matter for IoT Devices
When it comes to IoT, security is the name of the game. Think about it—your smart fridge, your security cameras, or even your smart doorbell could be vulnerable if not properly secured. A hacker gaining access to one of these devices can wreak havoc on your network, steal sensitive data, or worse.
SSH, or Secure Shell, is your best friend here. It provides a secure way to access and manage remote devices. But connecting IoT devices over SSH isn't always straightforward, especially when you're dealing with firewalls, NATs, and other network barriers. That's where P2P (peer-to-peer) SSH comes in handy.
Understanding SSH and Its Role in IoT
SSH is like a digital lock that keeps your data safe while it travels between devices. It encrypts your communications, ensuring that even if someone intercepts your data, they won't be able to make sense of it. For IoT devices, this is crucial because they often communicate over public networks.
- Scott Wapner Cnbc Wife The Untold Story Behind The Man And His Partner
- Subhashree Sahu Mms The Story That Sent Shockwaves Across India
- SSH encrypts data, making it unreadable to unauthorized users.
- It authenticates users and devices, ensuring that only trusted parties can access your network.
- SSH can be configured to work across firewalls, making it ideal for remote IoT setups.
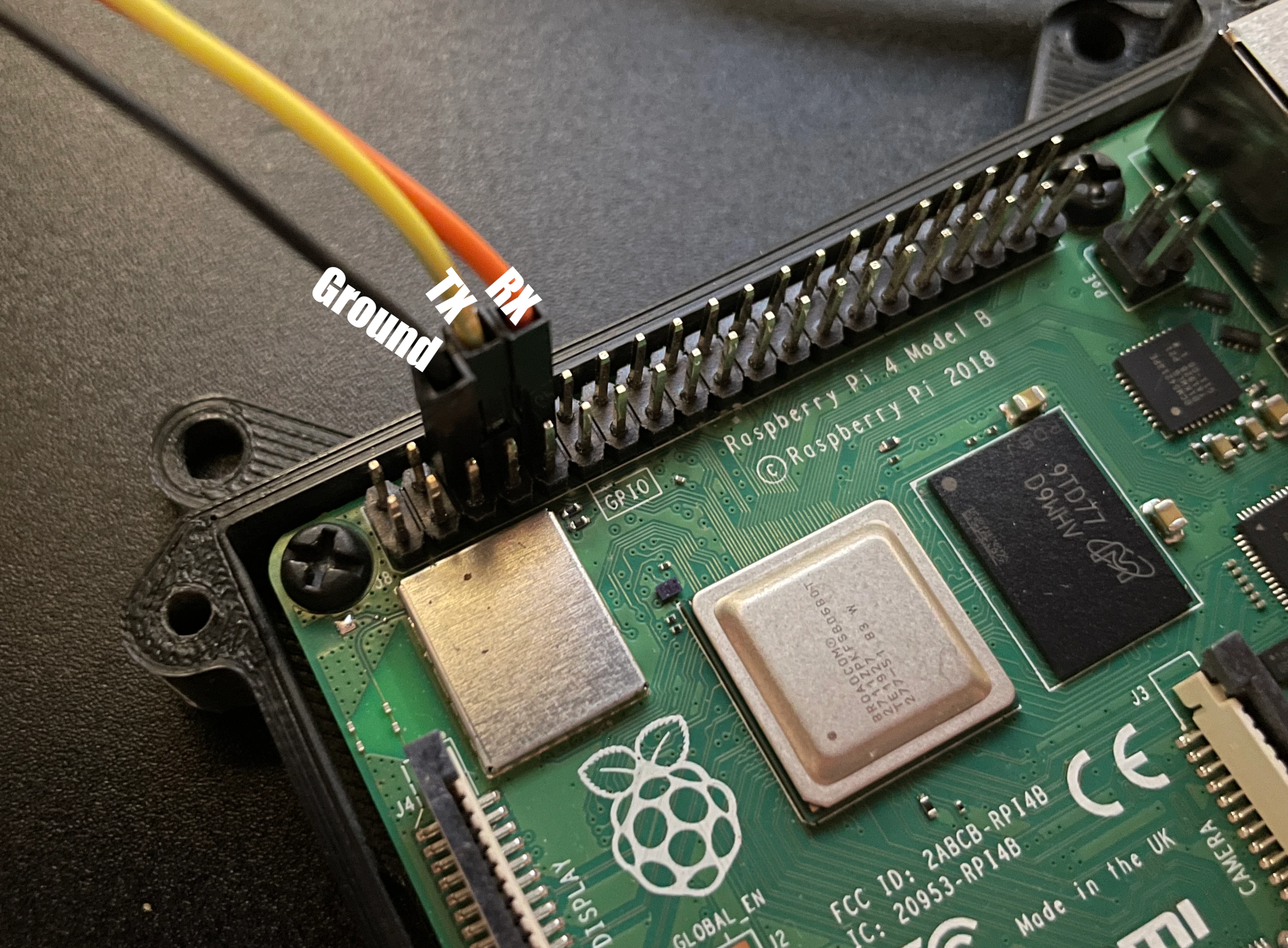
Setting Up SSH on Your Raspberry Pi
Before we dive into P2P connections, let's first set up SSH on your Raspberry Pi. This is the foundation of everything we'll be doing. Don't worry if you're new to this—it's easier than it sounds.
Step 1: Enable SSH on Raspberry Pi
Enabling SSH on your Raspberry Pi is as simple as flipping a switch. Here's how you do it:
- Power off your Raspberry Pi and insert the SD card into your computer.
- Create a file named "ssh" (no extension) in the boot partition of the SD card.
- Put the SD card back into your Raspberry Pi and boot it up. SSH should now be enabled.
Step 2: Configure SSH Settings
Now that SSH is enabled, let's tweak some settings to make it more secure. Open the terminal on your Raspberry Pi and type:
sudo nano /etc/ssh/sshd_config
Here, you can change settings like disabling root login, changing the default port, and enabling key-based authentication. These small changes can significantly boost your security.
Introducing P2P SSH for Remote Connections
Peer-to-peer SSH is a game-changer for IoT projects. Instead of relying on traditional client-server setups, P2P SSH allows devices to connect directly, bypassing firewalls and NATs. This makes it perfect for remote IoT deployments.
How Does P2P SSH Work?
In a typical SSH setup, you connect to a server from a client. But in P2P SSH, both devices act as peers, establishing a direct connection. This eliminates the need for a central server, making it faster and more secure.
- P2P SSH uses techniques like NAT traversal to bypass network barriers.
- It relies on public key cryptography to authenticate devices.
- The connection is encrypted end-to-end, ensuring data privacy.
Choosing the Right Tools for P2P SSH
Not all tools are created equal when it comes to P2P SSH. You'll want to choose ones that are lightweight, secure, and compatible with Raspberry Pi. Here are a few options:
Tool 1: ngrok
ngrok is a popular tool for creating secure tunnels to your Raspberry Pi. It's easy to set up and works great for quick testing and development.
Tool 2: PageKite
PageKite is another great option for P2P SSH. It allows you to expose your Raspberry Pi to the internet without modifying your router settings.
Tool 3: autossh
autossh is a robust tool that automatically restarts SSH connections if they drop. It's perfect for maintaining a stable connection to your IoT devices.
Securing Your P2P SSH Connections
While P2P SSH is inherently more secure than traditional setups, there are still steps you can take to further protect your IoT devices.
Tip 1: Use Strong Passwords
This one's a no-brainer. Weak passwords are a hacker's dream. Use strong, complex passwords and change them regularly.
Tip 2: Enable Key-Based Authentication
Key-based authentication is much more secure than password-based authentication. It uses public and private keys to authenticate devices, making it nearly impossible for hackers to gain access.
Tip 3: Limit Access
Only allow trusted devices to connect to your Raspberry Pi. Use firewall rules and SSH settings to restrict access to specific IP addresses.
Real-World Applications of P2P SSH
P2P SSH isn't just a theoretical concept—it has real-world applications in various industries. Here are a few examples:
Application 1: Smart Home Automation
With P2P SSH, you can remotely control and monitor your smart home devices. From adjusting the thermostat to checking your security cameras, everything can be done securely from anywhere in the world.
Application 2: Industrial IoT
In industrial settings, P2P SSH can be used to monitor and manage remote sensors and machines. This ensures that everything is running smoothly and reduces downtime.
Application 3: Agriculture
Farmers are using IoT devices to monitor soil moisture, weather conditions, and crop health. P2P SSH allows them to access this data remotely, making it easier to make informed decisions.
Troubleshooting Common Issues
Even with the best tools and configurations, issues can still arise. Here are some common problems and how to fix them:
Issue 1: Connection Refused
If you're getting a "connection refused" error, check your SSH settings and firewall rules. Make sure the SSH service is running and that your firewall isn't blocking the connection.
Issue 2: Key Authentication Failed
This usually happens when there's a problem with your SSH keys. Double-check that your public key is correctly added to the authorized_keys file on your Raspberry Pi.
Issue 3: Slow Connections
Slow connections can be caused by a variety of factors, including network congestion or poor SSH configuration. Try optimizing your SSH settings or using a faster network.
Conclusion: Securely Connect Remote IoT Devices with Confidence
There you have it—everything you need to know about securely connecting remote IoT devices using P2P SSH on Raspberry Pi. By following the steps in this guide, you can create a robust, secure setup that'll keep your IoT devices safe from prying eyes.
But don't stop here! The world of IoT is constantly evolving, so stay curious and keep learning. And if you found this guide helpful, don't forget to share it with your friends and colleagues. Together, we can make the IoT world a safer place!
Now it's your turn. Have you tried P2P SSH for your IoT projects? What challenges did you face? Share your thoughts in the comments below!
Table of Contents
- Why Secure Connections Matter for IoT Devices
- Setting Up SSH on Your Raspberry Pi
- Introducing P2P SSH for Remote Connections
- Choosing the Right Tools for P2P SSH
- Securing Your P2P SSH Connections
- Real-World Applications of P2P SSH
- Troubleshooting Common Issues
- Conclusion
- Charli Damelio Nude The Truth Behind The Viral Sensation
- Unveiling The Truth About Yumi Eto Nude Facts Myths And Everything You Need To Know

How to Connect via SSH to a Raspberry Pi Tony Teaches Tech
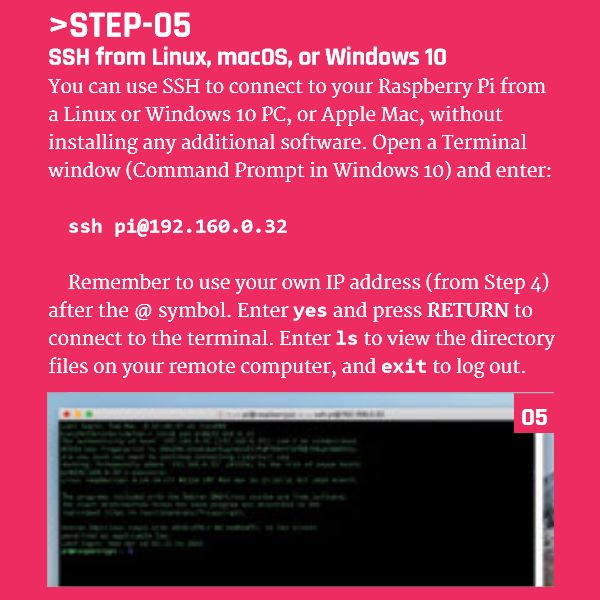
Connect to Your Raspberry Pi With SSH From Linux, macOS, or Windows 10
How To Securely Access Your Raspberry Pi Using Ssh Port ACCDIS